This article explores how five important emerging trends involving Shadow IT, AI, cybersecurity and regulation could have serious implications for banks and financial institutions and their operational resilience during the post COVID period and expected e-commerce boom. Understanding them is essential to appreciate the complex cybersecurity and operational resilience risks now posed to the financial sector.
1. Deep Recession and E-commerce Boom?
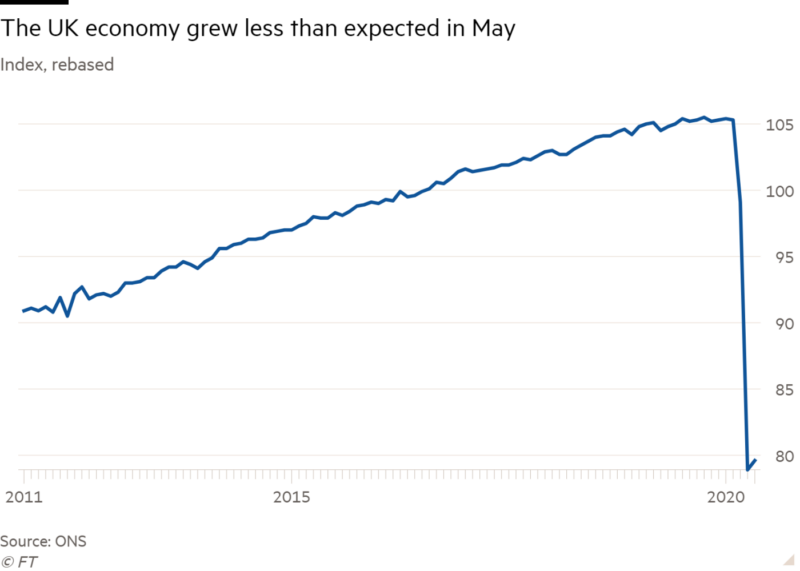
As the UK begins to ease out of lockdown, along with other parts of the world, a new global crisis looms – a recession, which dwarfs that of the 2008 financial crisis and is according to the World Economic Forum currently forecast to cause the worst global crisis since World War II. However, unlike World War II, as the Financial Times (1) writes, the post COVID economic recovery will also be largely characterised by permanent shifts in consumer behaviour, fueling a boom in e-commerce.
This boom is set to reach US$6.07 trillion in 2024, growing at a CAGR of 11.34% for the period 2020-2024 (2), largely due to the exponential increase in connectivity and its integration with existing systems and commerce alongside changes in our behaviour.
A recent report by Accenture (3) revealed that there was a 50% decrease in cash usage during the peak of the European lockdown in 17-25th March 2020. This is significant for the long-term, as the report also projected that there will be a 30% decline in cash usage in Europe in 2020. Payment merchant giants such as Visa have been actively encouraging transport networks and legislators to ease restrictions imposed on contactless payments in a bid to boost consumer spending.
As Forbes writes (4) “Banks have adapted to the crisis and change in consumer behaviour by accelerating their digital transformation processes to facilitate efficient streamlined working practices to serve their customer’s needs during the course of the pandemic.” However, these intense structural and cultural changes in the way financial institutions operate also reveal weaknesses in their cybersecurity practices.
For example in the U.S – where 70% of the economy is defined by consumer spending, cyberattacks against the financial sector rose by 238% (5) between February and April. Meanwhile in the UK, attacks spiked by 38% between February and March (6). And while Australia may be in the news now due to the recent broad and sophisticated cyber-attack by a state-backed actor,(7) Australian banks had already been targeted in February by a group threatening to launch denial-of-service attacks.
These patterns demonstrate that hackers are clearly investing time and resources to launch sophisticated, high-impact attacks.
With a new recession and associated potential financial shocks looming it would frankly be reckless of banks to not invest in scaling up their cybersecurity operations. The next five years will almost certainly be difficult. Therefore it is important that financial institutions invest time and money now to adjust to consumer needs and become more resilient to ride out the dangers associated with our post COVID world.

2. Shadow IT systems
By exploring the risks posed by cloud-based shadow IT systems it is easy to see just how easily financial data can be compromised. Shadow IT systems are not a new phenomenon. In 2016 The Financial Conduct Authority (FCA)’s (7) guidance on outsourcing IT to the cloud marked a turning point in which the financial industry accelerated the pace of it’s ‘digital transformation’.
Due to the pandemic however organisations have had little choice but to increase their use of shadow IT systems to allow for the smooth running of operations. Shadow IT describes cloud services, software or hardware used by a department or individual, often without the knowledge of the IT or security group within the organization. Shadow IT systems are great for business continuity in that they allow organisations to boost capacity to handle data, providing them with an unrivalled level of agility, security and scalability.
However the cybersecurity risks posed by Shadow IT systems highlight why banks should err on the side of caution. Broadly risks are associated with discrepancies in cybersecurity compliance processes within institutions. This can be caused by the inconsistency and often large number of administrative staff involved around compliance procedures, which further exposes sensitive data to hackers due to the larger attack surface available to them to exploit.
This can lead to a greater number of oversights when compliance procedures are reviewed along with larger attack surfaces because the ‘leadership and command’ process is no longer centralised. Finally, the sheer number of applications available to organisations allow for poor visibility into their usage. The on-going shortage of cybersecurity experts available, required to monitor the usage of these applications under a decentralised system, means that sensitive information is difficult to protect.

3. Improving leadership methods within Infosec
In a recent panel discussion Not if but when: Are we prepared for the next big data breach at the CogX virtual conference, Becky Pinkard – CISO – Aldermore Bank stressed that more conversations need to be had between senior IT leaders around the nature of risks that organisations are currently prepared for. Identifying this now is a first step in changing management structures and practices to adapt to a post corona world. Rather than transferring risk or relying on external organisations to identify, assess, mitigate and manage cyber threats, organisations must do this themselves. Such a move is a delicate balancing act between working within a decentralised system to increase financial institutions’ consumer bases whilst also having well defined, practical, cyber threat mitigation strategies.
Meanwhile further down the hierarchy, the human side of cyber defence practices also need to be re-evaluated. Common yet overlooked issues such as employee dissatisfaction and naivety around security related matters should be identified early to prevent data breaches. This matters because more than a third of data breaches involve internal actors, according to a 2019 Verizon analysis of more than 40,000 incidents.
According to Michael Beck – Global Head of Threat Analysis – Darktrace, one way to adapt to technological advancement is to have more interoperable roles available within financial organisations to allow for greater foresight around how to scale technologies using different platforms to manage data. Again rather than outsourcing data management functions to external sources, there is an opportunity to learn from tech-for-good organisations to understand how they keep data safe. The key questions for ’interoperable leaders’ to maintain the safety of financial data would be to focus on questions around: Where does the data sit and where it will be accessed? Does this organisation have an adequate balance of data analytics and cybersecurity skills set required to manage the volume of data? Based on this, it is inevitable that banks will require new technical solutions.
4. Integrating AI for Cyber Threat Intelligence (CTI) into financial institutions’ operational resilience
One solution that will save financial organisations time and money in the longer term is to reduce the time taken by analysts to interpret new, incoming threat warnings. Automating the process of reviewing cyber threat intelligence reports makes sense, given the large volume of data that cyber analysts have to contend with. Elemendar’s AI for CTI engine automates the reading and translation of CTI from human authored unstructured text and documents into machine-readable and actionable data output as STIX 2.0 and incorporating MITRE ATT&CK™. This enables all CTI to be analysed and immediately acted on in minutes, not hours, drastically reducing the window of vulnerability. This enables analysts to spend their time doing more crucial work to better protect against threats.

5. Regulation
In December the Bank of England, Prudential Regulation Authority and the Financial Conduct Authority published a shared policy summary and co-ordinated consultation paper designed to enable organisations to boost their operational resilience. However, despite this guidance, the issue of concentrated risk has only increased as a result of the demand for cloud services, which raises further security concerns over the protection of financial data during the pandemic and beyond as practical and security considerations have been overlooked.
In this sense, “regulators are concerned about what they call concentration risk, which is essentially putting all your eggs in one basket” according to Daniel Read, a partner with the technology and IP division of financial services-focused law firm TLT LLP.
Clearly, to avoid potential economic damage due to the cracks in their cybersecurity practices, banks should review the impact of their decentralised IT systems and invest in their operations with new, relevant technology now.
Elemendar’s AI for Cyber Threat Intelligence engine reads and translates human authored CTI feeds into machine-readable and actionable data (STIX2 inc. MITRE ATT&CK™). This saves significant time and money and better protects your whole organisation from threats. Try our free trial here.Elemendar’s AI for Cyber Threat Intelligence engine reads and translates human authored CTI feeds into machine-readable and actionable data (STIX2 inc. MITRE ATT&CK™). This saves significant time and money and better protects your whole organisation from threats. Try our free trial here.