Ever read a classic crime novel? The villain’s identity only becomes clear after a couple of plot twists and turns. Attribution in Cyber Threat Intelligence (CTI) sometimes feels like that kind of detective work. For the cyber-threat analyst, gathering clues and assigning responsibility for cyber-attacks to specific individuals, threat groups or nation states is not easy, or quick.
Technical analysis is needed, as well as examination of tactics, techniques, and procedures (TTPs), and—finally—covert intelligence to gather details. But the multitude of names that CTI vendors assign to each suspect adds an extra, anxiety-inducing aspect to the process.
Ideally, we’d all agree on a standardised naming convention. But until the distant future arrives with that convention (if it ever does), let’s focus on some coping mechanisms for the CTI detective.
Cyber-Threat Aliases: Is No One Who They Seem?
Think about “APT29”, aka Dark Halo (according to Volexity), StellarParticle (CrowdStrike), YTTRIUM (Microsoft), and SolarStorm (Palo Alto Unit 42). We’re talking about a single threat group, but all those CTI vendors create aliases linked to their own naming schemes. This is because each vendor defines a threat group in its own way and chooses names to fit their definitions. Great for them, bad for us; with a sea of aliases, waves of confusion often engulf intelligence practitioners.
The average analyst could easily mistake the various names above as belonging to five unique threat groups, each with its own long history of successful attacks. To that analyst, the number of active threat groups seems far greater than in reality. Can you see how severely distorted the threat landscape can become, if we can’t easily zero in on a single perpetrator?
Uniformity in naming attackers would enable practitioners to interpret new threat behaviours, TTPs and campaigns with a bit more ease.
Looking for Clues: Cut Through the CTI Noise
Each CTI vendor has (presumably) built a reputation with its clients and market base; it’s naïve to assume they would suddenly change their naming style just because a standard is introduced. If anything, we can imagine them falling into an “N+1” loop of standardised naming conventions, like that shown in Figure 1.
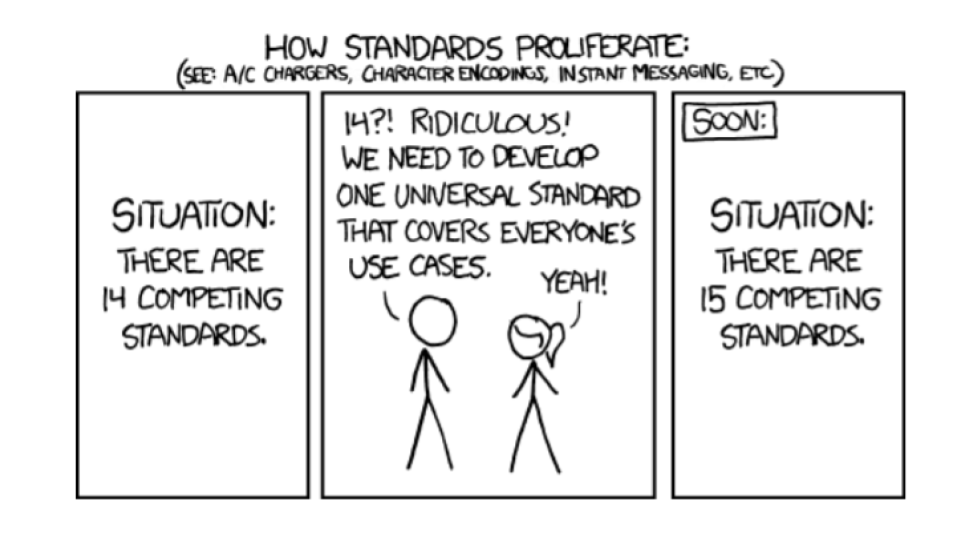
Figure 1: A plausible evolution scenario for threat actor/group naming standards
So, let’s assume no standard is set to emerge, and instead focus on reducing the ‘noise’ practitioners face when they’re attributing cyber-threat activity. We’ve found a few stellar resources:
- APT Groups and Operations is an online initiative by a few contributors who recognised the complexity of attribution and created an open-source spreadsheet for practitioners to cross-reference aliases. A recent update added Microsoft’s renaming taxonomy.
- STIX’s Intrusion Set can be loosely defined as threat activity that can be attributed to a threat actor. If you come across various reports about similar behaviour about actors with different aliases, this STIX object could help interpret new TTPs and campaigns.
- A forensic or linguistic approach is a more abstract form of attribution. Ultimately, malware is a form of code and its author would have a habitual style of coding. Because their motives can be captured in that style, researchers have identified over 1,000 characteristics to analyse and attribute code to an author.
Structuring Data to Narrow the Pool of Suspects
Attribution is one of the most technically complex processes in CTI, and its biggest challenge. That’s not going to change. When done well, attribution rewards the practitioner with much-needed clarity. But it’s foolish to rely on name uniformity to achieve that clarity.
The resources above illustrate that structuring data points is essential to clearing the mists of identity. When structure is introduced to data, you can at least have a single repository of information – not facts scattered across cyberspace. A single source of knowledge that empowers cross-referencing saves time. Elemendar’s flagship software product READ. is a power tool for this process. Using automation and Machine Learning to add structure to unstructured CTI data using the STIX format, READ. provides the base from which common CTI activities such as Threat Hunting and Attribution are conducted. Even a fictional detective would find that kind of resource useful.