READ.
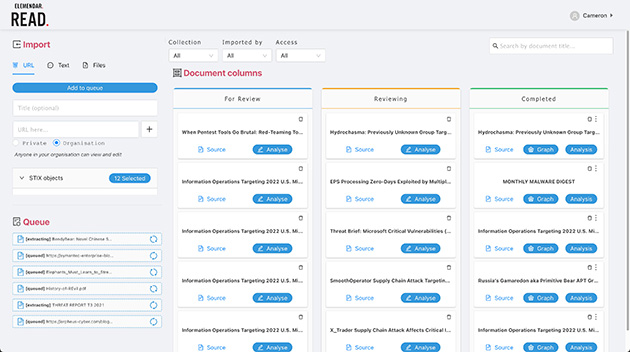
READ. processes human-authored, unstructured CTI reports into structured CTI data. This machine-readable data can then be fed directly into a TIP or defensive systems for security analysts to operationalise. Data Extraction, STIX Processing and Output is completed seamlessly within READ. allowing analysts to pivot from extensive CTI documents to valuable, actionable data within seconds.
Data Extraction.
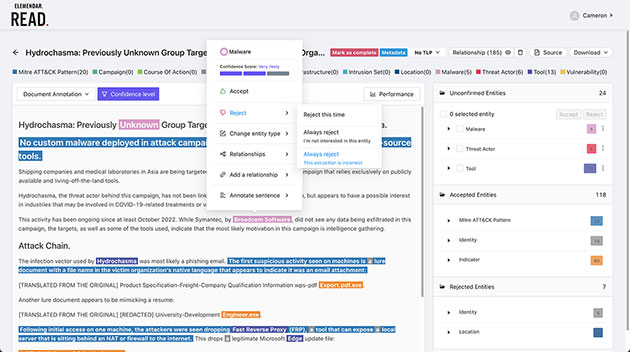
Elemendar’s READ. application extracts CTI data from URLs, PDF files and free form text. Graphics and images are also retained for context in the annotation view.
Output.
Outputs are user-configurable and can include MISP or TAXII/TAXII2 servers, supporting a STIX JSON file. READ. also offers a RESTful API which enables users to full integrate the application into existing workflows for complete automation & orchestration of CTI processing. We also offer tailored output solutions for your organisational needs.
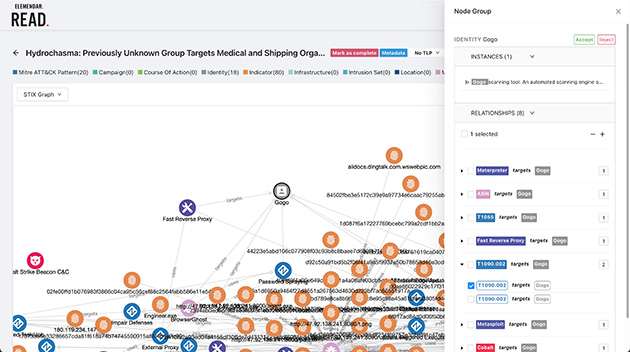
STIX Processing.
The extracted text is analysed using Elemendar’s proprietary, machine learning-powered Natural Language Processing engine. READ. extracts and categorises entities from the unstructured CTI using the STIX standard. Text is also processed, extracted and matched against the MITRE ATT&CK framework to provide relevant attack patterns. Lastly, relationships between these objects are visibly outlined for the user to identify.